From charlesreid1
- 1SSH Service Info
- 1.1Metasploit SSH Exploits
- 2Brute Force ssh_login
- 3Private Key ssh_login_pubkey
- 3.1Obtaining Private Key
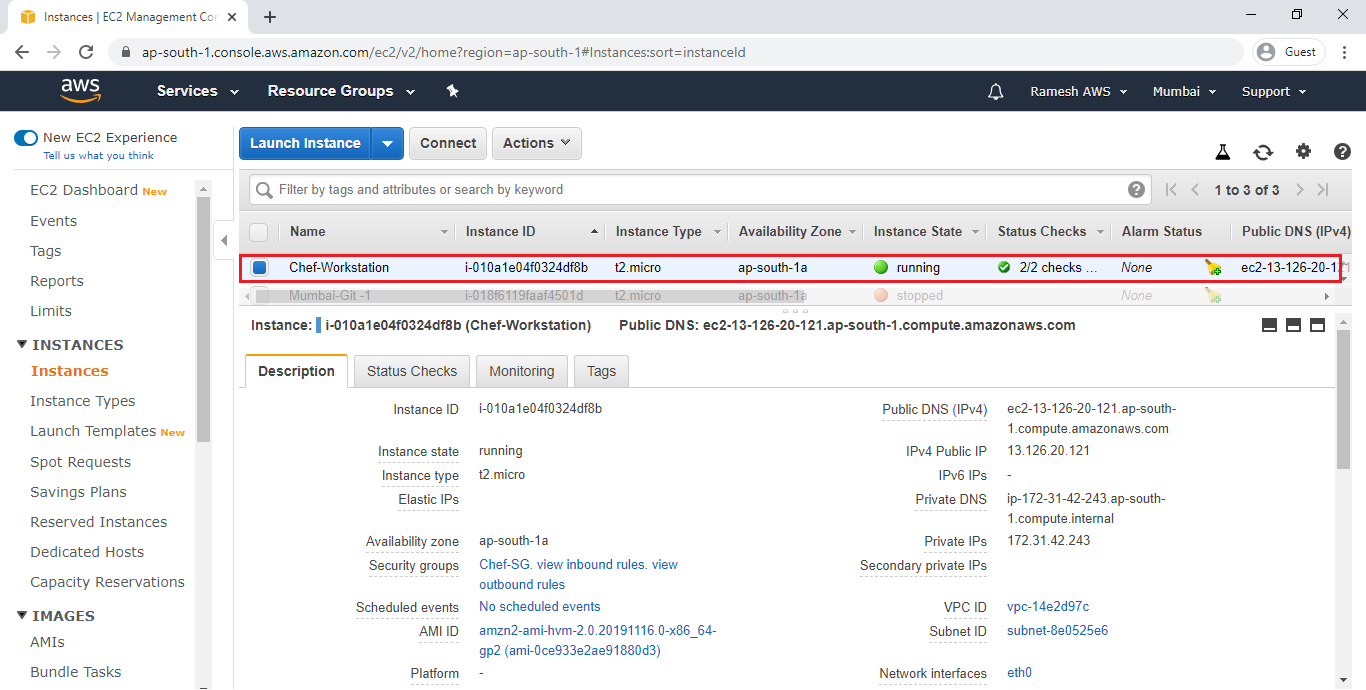
First, a reminder of the information nmap returned about the SSH service after a port scan:
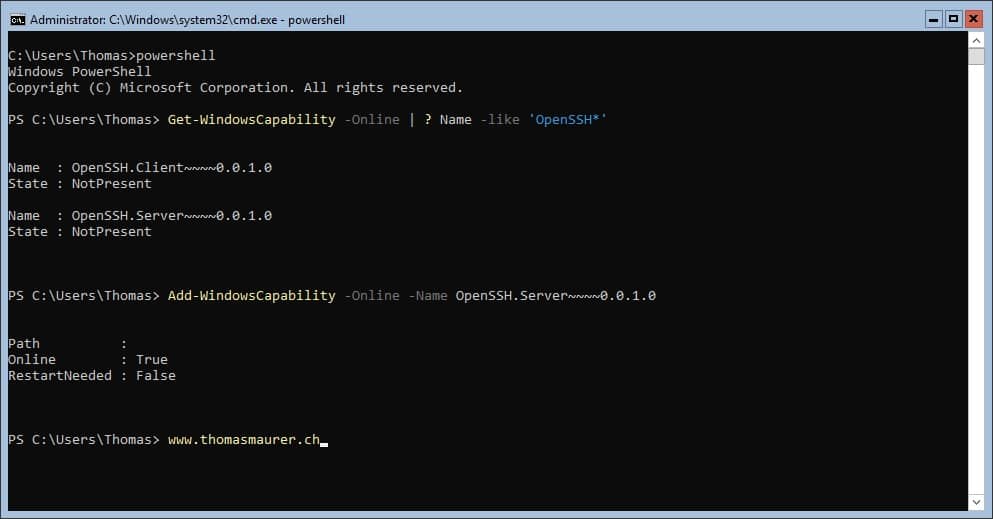
OpenSSH will begin to install and configure itself for your system. At this point, openssh is setup and configured for your system. To try this out, open up a command prompt (cmd.exe) and try: ssh -v (For OpenSSH 6.3 and below) ssh -V (For OpenSSH 6.4 and above).
- Start studying 15.6.7 - OpenSSH (Practice Questions). Learn vocabulary, terms, and more with flashcards, games, and other study tools.
- Watch the Long Play version at Debian Wheezy 2015-01-31 3.18You only have to do this if using.Wheezy.There be no need to.
This server isn't using the 1.0 protocol, which is hopelessly broken and easy to defeat. This means getting past SSH will be (at least) mildly challenging.
Metasploit SSH Exploits
Two SSH attacks using metasploit:

- ssh_login
- ssh_login_pubkey
Metasploit ssh_login
The first attack is ssh_login, which allows you to use metasploit to brute-force guess SSH login credentials.
- Module name is
auxiliary/scanner/ssh/ssh_login
Link: https://www.offensive-security.com/metasploit-unleashed/scanner-ssh-auxiliary-modules/
Metasploit ssh_login_pubkey
The second attack requires a private key. If you do gain access to the private SSH keys on a victim machine, you can attempt to authenticate with a large number of hosts and services using that private key.
- Module name is
auxiliary/scanner/ssh/ssh_login_pubkey
Link: https://www.offensive-security.com/metasploit-unleashed/scanner-ssh-auxiliary-modules/
We already covered how to brute force the login with Hydra, Metasploitable/SSH/Brute Force
Did you know you can also brute force an SSH login with Metasploitable? Use the auxiliary/scanner/ssh/ssh_login module.
Setting Up the Attack
We will use the module auxiliary/scanner/ssh/ssh_login:
Set this to run on the Metasploitable virtual box target:
Running the Attack
Now run the attack:
Houston, We Have A Shell
At this point, we can create a session with the machine that we compromised. Logged in as user msfadmin:
If you manage to get your hands on the victim's private key, the auxiliary/scanner/ssh/ssh_login_pubkey module is for you!
This module uses the private key to do two things:
- Get access to the victim machine
- Get access to any machines that trust the victim's private key (must be listed in the SSH files of the victim machine)
Obtaining Private Key
To carry out this attack, you will need to have access to the file system, and/or be able to mount the remote file system (which, on Metasploitable, happens to be possible!): see Metasploitable/NFS
Once you've got access to the file system, you'll grab a copy of the remote machine's private keys, and use them together with Metasploit to obtain access to the machine.
(Note that you could also plant your keys on the target, by adding your public SSH keys onto the target machine's list of trusted machines, but this technique would restrict you to a particular machine, wile the Metasploit method is portable and less intrusive.)
To snatch the target's private key:
Now you have a copy of the msfadmin account's private SSH key.
Metasploit We'll use Metasploit to turn this into access to the remote machine.
This key is also useful for impersonating the target when connecting to OTHER remote machines.
Planting Private Keys
An alternative method to gain access, although it is not useful for gaining access to any machines other than the victim machine, is to GENERATE a public/private SSH key pair from the attacker machine, and copy the PRIVATE key over to the remote machine. (Using the public key and the above-mentioned technique would be easier, but it's worth mentioning at least.)
To plant your private keys on the remote machine, you'll need write access to the target user's home directory. You'll generate a public SSH key from the attacker machine, the machine you want to have access WITH, and add it to the other machine's ~/.ssh/authorized_keys.
This presumes the .ssh directory exists. If it doesn't exist, you can make it, and tamper with the filesystem.
Setting Up the Attack
Here's info on the auxiliary/scanner/ssh/ssh_login_pubkey module in Metasploit, which will carry out the attack:
Set some options, such as the private key file, the username to log in with, and the remote host:
Running the Attack
Execute the attack, to use the remote machine's private key to gain access to the remote machine:
Success - we've got a session.
Getting a Shell
Now we can use the sessions command to utilize the information we just found and set up an interactive session.
We could create more mischief, by copying everyone else's private SSH keys and SSH connection histories, potentially giving us passwordless access to additional machines.
We could also get busy with post-exploit activities.
See https://www.offensive-security.com/metasploit-unleashed/scanner-ssh-auxiliary-modules/
Sasem co.,ltd & sigmacom driver download for windows.

Openssh 6.7p1 Exploit
Openssh 6.7p1 Exploit
